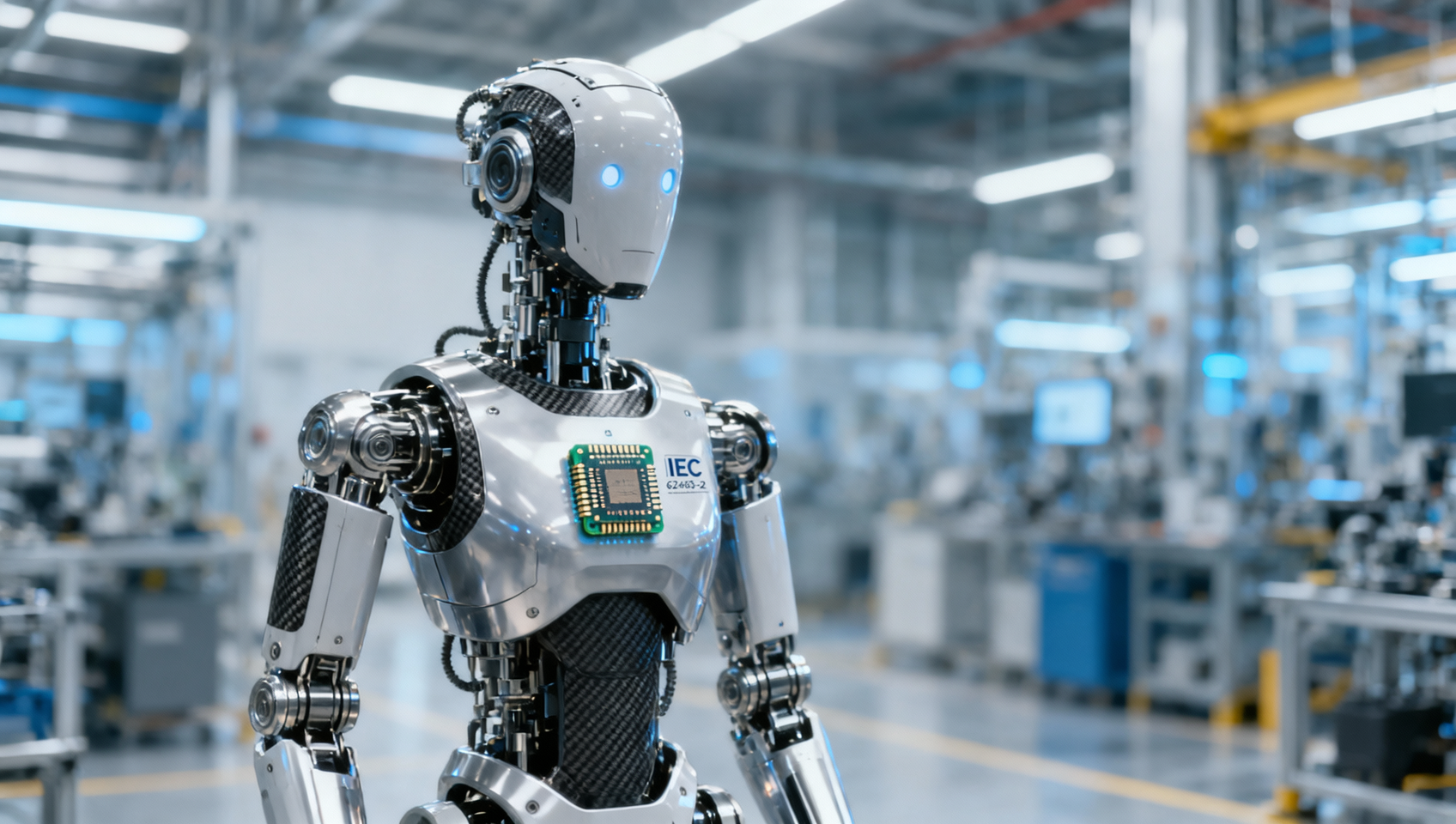
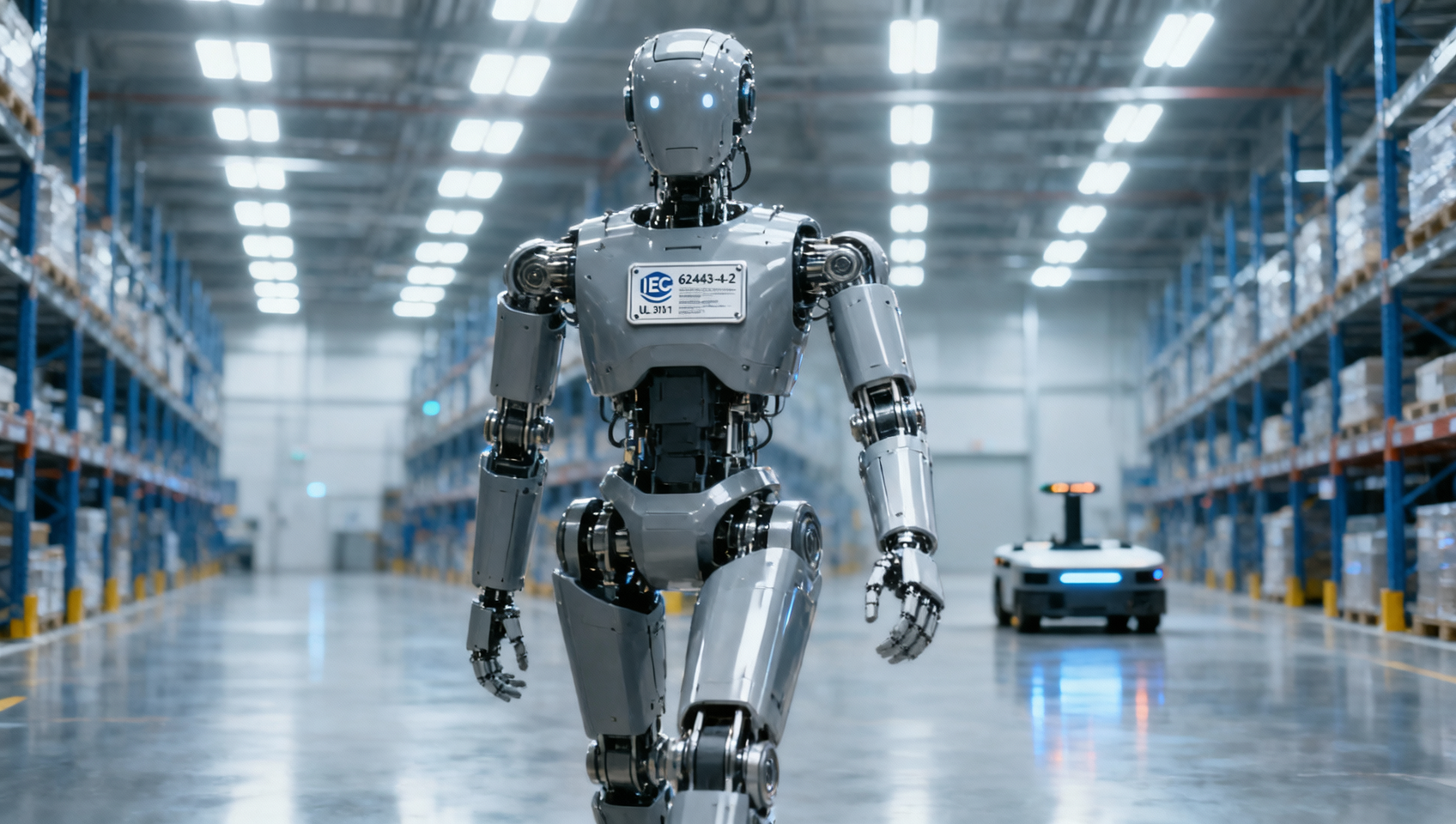
IEC 62443-4-2 Certification Becomes Mandatory for Humanoid Robots Entering EU, UK & GCC Markets
On May 9, 2026, the European Union Agency for Cybersecurity (ENISA) and Germany’s TÜV Rheinland jointly published updated guidance mandating IEC 62443-4-2 compliance for all humanoid robots—including embodied AI terminals—as a prerequisite for market access in the EU, UK, and Gulf Cooperation Council (GCC) free trade partner countries starting Q3 2026. This development directly impacts Chinese OEMs’ export timelines and software architecture decisions, as non-certified products will be ineligible for dual-signature CE Declaration and Cybersecurity Declaration.
Event Overview
On May 9, 2026, ENISA and TÜV Rheinland issued official guidance confirming that IEC 62443-4-2—specifically addressing secure product development lifecycle requirements for industrial automation and control systems—shall serve as a mandatory conformity requirement for humanoid robots entering the EU, UK, and GCC free trade agreement countries beginning in Q3 2026. The guidance explicitly states that successful certification is required to complete both CE marking and the new Cybersecurity Declaration under the EU Cyber Resilience Act (CRA) framework.
Industries Affected by Segment
Direct Exporters (OEMs & System Integrators)
Chinese and other non-EU manufacturers exporting humanoid robots face immediate impact: delivery schedules must now accommodate IEC 62443-4-2 certification lead times (typically 6–12 months), and software development workflows must align with certified secure development lifecycle (SDLC) practices. Failure to obtain certification pre-Q3 2026 blocks CE+Cybersecurity Declaration issuance—effectively halting customs clearance and market placement.
Embedded Software & Firmware Developers
Suppliers responsible for robot operating systems, safety-critical firmware, or network-facing modules are affected because IEC 62443-4-2 requires documented evidence of threat modeling, secure coding standards, vulnerability management, and third-party component vetting. Development teams must revise internal SDLC documentation and toolchains—not just implement technical controls—to meet audit requirements.
Contract Manufacturers & Electronics Assemblers
Manufacturers handling final assembly, firmware flashing, or hardware-software integration must demonstrate traceability and configuration control per IEC 62443-4-2 Annex A. This includes maintaining version-controlled build environments, signed firmware images, and auditable records of supply chain components—adding operational overhead beyond traditional ISO 9001 or IEC 62443-3-3 compliance.
Certification & Compliance Service Providers
Third-party labs and consultants offering cybersecurity certification services face rising demand—but also heightened scrutiny. The guidance specifies that only certification bodies accredited under EN ISO/IEC 17065 and authorized for IEC 62443-4-2 assessment may issue valid reports. Providers lacking this scope must either seek accreditation or refer clients to qualified partners.
Key Focus Areas and Recommended Actions
Monitor Official Updates from ENISA and National Market Surveillance Authorities
While the May 9, 2026 guidance establishes intent, formal incorporation into EU harmonized standards lists—and national implementation decrees in the UK and GCC members—remains pending. Stakeholders should track updates via ENISA’s CRA Implementation Portal and national competent authorities’ notifications, particularly regarding transitional arrangements or phased enforcement timelines.
Prioritize Certification Readiness for High-Volume or Flagship Models
Given resource constraints in testing capacity and engineering bandwidth, companies should identify which humanoid robot models are slated for EU/UK/GCC launch in Q3–Q4 2026 and initiate gap assessments against IEC 62443-4-2 Clauses 5–9 immediately. Focus on design documentation, secure boot mechanisms, and update integrity verification—areas most frequently cited in preliminary audits.
Distinguish Between Policy Signal and Enforceable Requirement
The May 9 guidance is not yet law but functions as binding administrative direction for notified bodies and market surveillance authorities. Its enforceability hinges on alignment with the EU Cyber Resilience Act’s delegated acts (expected Q2 2026). Until then, voluntary conformance supports due diligence—but does not substitute for formal certification post-Q3 2026.
Initiate Cross-Functional Alignment on Documentation and Traceability Protocols
Engineering, QA, procurement, and regulatory affairs teams must jointly define standardized templates for threat modeling reports, secure coding checklists, SBOM (Software Bill of Materials) generation, and firmware signing logs. Early alignment avoids bottlenecks during audit preparation and ensures consistency across product lines.
Editorial Perspective / Industry Observation
Observably, this guidance signals a structural shift—not merely an incremental regulatory addition. It marks the first time a functional safety-adjacent standard (IEC 62443-4-2) has been formally extended to embodied AI systems without requiring separate AI Act alignment. Analysis shows the move reflects growing convergence between industrial control system security expectations and autonomous physical agent governance. From an industry perspective, it is more accurately understood as a policy signal with near-term operational consequences: while full legal codification remains pending, market gatekeepers—including customs brokers, notified bodies, and platform distributors—are already adjusting intake criteria. Continued attention is warranted as UK and GCC members finalize their own implementing rules, which may diverge in scope or timing.

Conclusion: This requirement underscores the accelerating integration of cybersecurity compliance into physical product market access—not as a standalone add-on, but as a foundational condition for commercial deployment. It does not represent a temporary hurdle but rather the institutionalization of secure-by-design principles for intelligent robotics in regulated markets. Currently, it is best understood as a binding operational threshold for Q3 2026 entry, rather than a distant regulatory horizon.
Source Attribution:
• European Union Agency for Cybersecurity (ENISA)
• TÜV Rheinland
Note: Formal transposition into national legislation by UK and GCC member states remains under observation and is not yet confirmed.
Get weekly intelligence in your inbox.
No noise. No sponsored content. Pure intelligence.