EU Mandates EN 303 645:2025 Cybersecurity Certification for IoT Imports from July 2026
On 6 May 2026, the European Union confirmed that the EN 303 645:2025 standard for cybersecurity of Internet of Things (IoT) devices will become fully mandatory for all imported IoT products entering the EU market as of 1 July 2026. This requirement directly affects manufacturers and importers in consumer electronics, smart home systems, industrial sensors, connected medical devices, and other networked hardware sectors — making timely compliance a critical operational priority.
Event Overview
On 6 May 2026, the European Union Agency for Cybersecurity (ENISA) and CENELEC jointly confirmed that EN 303 645:2025 — the harmonised standard for cybersecurity of consumer and industrial IoT devices — will be enforced across the EU from 1 July 2026. From that date, all IoT devices with network connectivity intended for placement on the EU market must undergo conformity assessment against this standard to obtain CE marking. Devices without valid certification will not be permitted to bear the CE mark and cannot be legally placed on the market. The scope covers both consumer and industrial IoT equipment. Chinese IoT manufacturers are required to complete penetration testing, firmware security audits, and establish documented vulnerability response processes within six months. EU-based importers must integrate certification status into their supplier qualification criteria.
Industries Affected
Direct Exporting Manufacturers (e.g., China-based IoT OEMs/ODMs)
These entities are directly responsible for demonstrating conformity before shipment. Non-compliance means inability to affix the CE mark — resulting in blocked market access. Impact manifests in extended time-to-market, increased pre-shipment validation costs, and potential redesign cycles for legacy firmware or insecure update mechanisms.
EU-Based Importers and Distributors
Under EU product liability and market surveillance rules, importers assume legal responsibility for CE conformity. They must now verify and retain technical documentation proving EN 303 645:2025 compliance — including test reports and vulnerability disclosure policies — as part of due diligence. Failure to do so may lead to enforcement actions, product recalls, or penalties under Regulation (EU) 2019/1020.
Contract Manufacturers and Firmware Developers
Suppliers providing firmware, secure boot modules, or over-the-air (OTA) update infrastructure are indirectly but materially affected. Their deliverables must support requirements such as secure default configurations, protected interfaces, and patchability — meaning contractual specifications and development workflows must be updated to reflect EN 303 645:2025’s technical clauses.
Supply Chain Verification Service Providers
Third-party labs, certification bodies, and audit firms offering conformity assessment services face rising demand for EN 303 645:2025-specific testing (e.g., credential hardening, insecure interface checks, update integrity verification). Capacity constraints and lead times for accredited assessments are expected to increase significantly ahead of the July 2026 deadline.
What Enterprises and Practitioners Should Monitor and Do Now
Track official interpretations and transitional guidance
Analysis shows that while the mandate date is fixed, CENELEC and national market surveillance authorities may issue non-binding application notes or Q&A documents clarifying scope boundaries — e.g., whether certain low-power, intermittently connected sensors fall under the regulation. Monitoring updates from the EU Commission’s NANDO database and ENISA’s dedicated IoT portal is recommended.
Prioritise high-volume and high-risk product categories
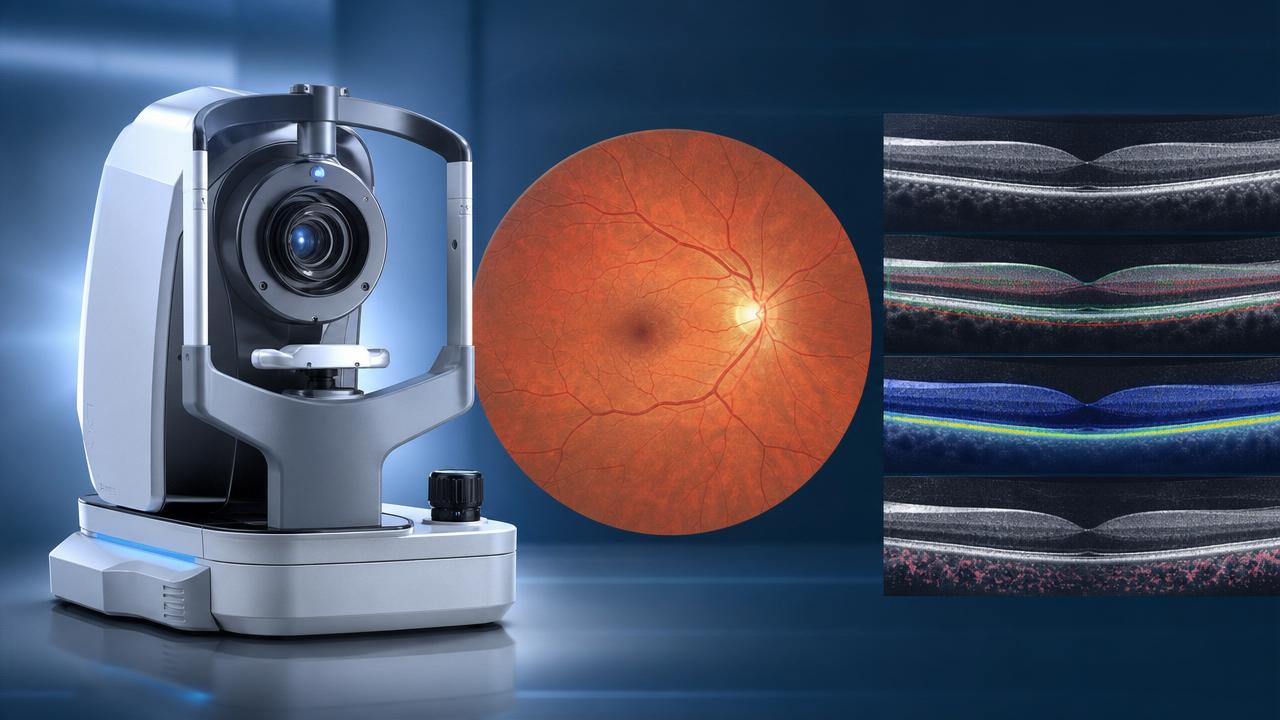
Observably, devices with remote administrative access, cloud-dependent functionality, or user-updatable firmware carry higher scrutiny risk. Companies should triage product portfolios to identify those requiring full certification first — particularly consumer-facing devices (e.g., smart cameras, voice assistants) and industrial gateways handling sensitive operational data.
Distinguish between regulatory signal and enforceable obligation
Current implementation requires formal certification only for new device models placed on the market after 1 July 2026. Analysis indicates that existing stock already lawfully placed on the EU market before that date remains unaffected — but no new units of that model may be introduced without certification. Businesses should audit inventory and shipment schedules accordingly.
Prepare supplier communication and procurement alignment
Manufacturers must initiate formal engagement with suppliers of critical components (e.g., Wi-Fi modules, OTA frameworks) to confirm their ability to support EN 303 645:2025-aligned security features. EU importers should revise supplier questionnaires and contractual annexes to require evidence of certification readiness — including timelines for test completion and documentation handover.
Editorial Perspective / Industry Observation
Observably, this mandate represents less an isolated policy shift and more the formalisation of an emerging baseline expectation: IoT devices must embed security-by-design principles before reaching end users. While EN 303 645:2025 itself is technology-neutral and risk-informed, its enforcement signals growing regulatory convergence — especially as it aligns closely with the upcoming EU Cyber Resilience Act (CRA) requirements for digital products. From an industry perspective, the July 2026 deadline functions primarily as a hard enforcement milestone rather than a soft guideline; however, its real-world impact will depend heavily on how consistently national market surveillance authorities apply penalties during the initial 12–18 months post-implementation.
Current more suitable understanding is that this is not merely a certification checkbox, but a structural recalibration of product development accountability — shifting emphasis from post-deployment patching to pre-market security assurance.
This development underscores a broader trend: cybersecurity compliance is evolving from optional best practice to non-negotiable market access condition — particularly for hardware with persistent internet connectivity.

The significance lies not in novelty, but in enforceability: for the first time, a harmonised standard explicitly defines minimum cybersecurity expectations for IoT devices across the entire EU single market — with direct consequences for design, testing, documentation, and supply chain governance.
Information sources: European Union Agency for Cybersecurity (ENISA), CENELEC, Official Journal of the European Union (as referenced in the 6 May 2026 joint announcement). Note: Ongoing monitoring is advised for any supplementary guidance documents issued by EU Member State market surveillance authorities or the European Commission’s Directorate-General for Communications Networks, Content and Technology (DG CONNECT).
Get weekly intelligence in your inbox.
No noise. No sponsored content. Pure intelligence.