US CPSC Proposes Mandatory Cybersecurity Labels for IoT Devices
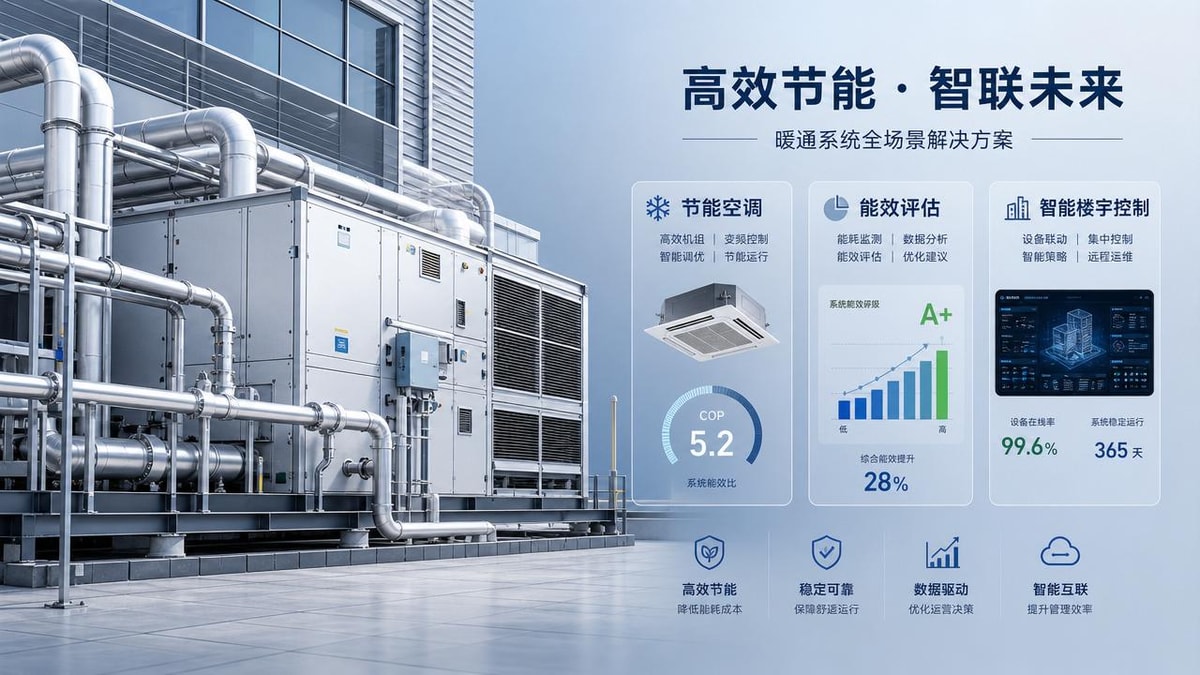
On May 6, 2026, the U.S. Consumer Product Safety Commission (CPSC) released the draft rule Cybersecurity Labeling Requirements for Internet-Connected Devices, proposing mandatory, verifiable cybersecurity labeling for all IoT devices sold in the United States—including smart home appliances, networked sensors, and edge gateways. This development directly affects exporters of IoT devices from China and other manufacturing hubs, as non-compliant products may face customs rejection or retail delisting. Companies involved in IoT hardware design, manufacturing, export compliance, and distribution—particularly those serving the U.S. market—should treat this as a near-term regulatory signal with tangible operational implications.
Event Overview
The U.S. Consumer Product Safety Commission (CPSC) published the Draft Rule on Cybersecurity Labeling for Internet-of-Things Devices on May 6, 2026. The draft requires that all IoT devices offered for sale in the U.S. carry a standardized, scannable label disclosing three verified attributes: firmware update mechanisms, vendor vulnerability response timeframes, and data encryption standards. The rule is scheduled to take effect in Q4 2026. No final version has been adopted; the draft is currently open for public comment.
Industries Affected by Segment
IoT Device Exporters & Brand Owners
Exporters placing branded or private-label IoT devices into the U.S. market will be legally responsible for label accuracy and verification. Impact includes added pre-market compliance validation steps, potential delays in customs clearance, and liability exposure if labeled claims are found inaccurate post-launch.
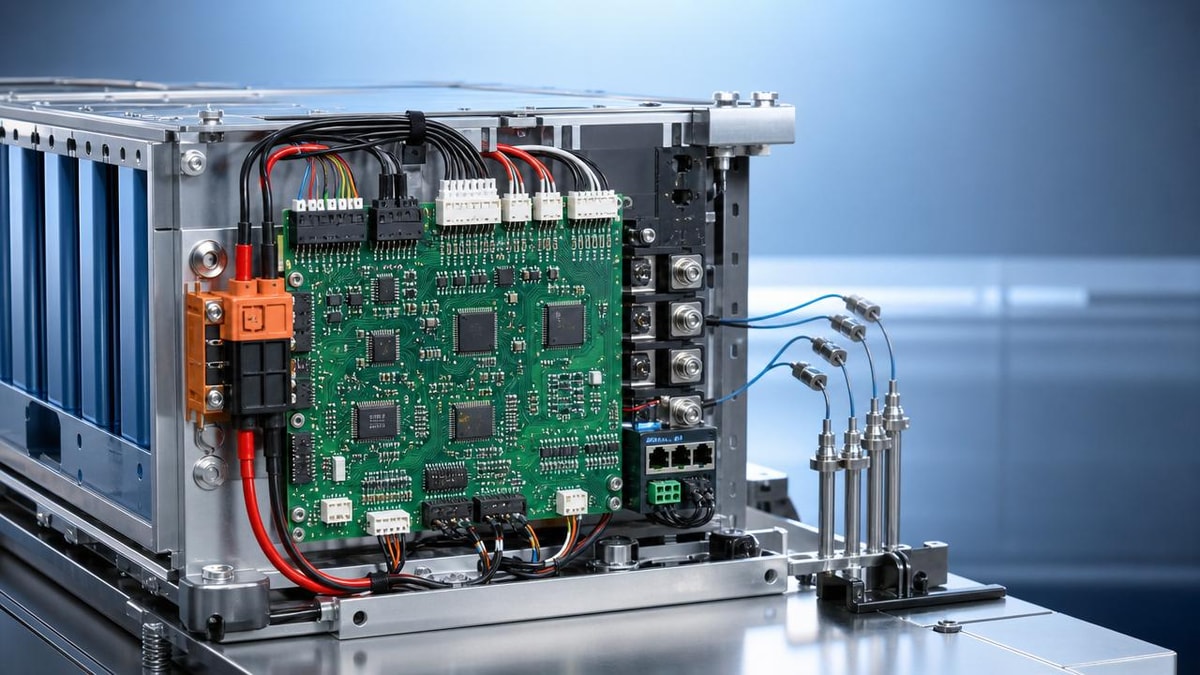
Contract Manufacturers & OEMs
OEMs producing IoT hardware for U.S.-bound brands must now support label-related technical documentation—such as firmware update logs, encryption implementation reports, and incident response SLA records. This introduces new documentation requirements into production handover processes and may affect factory audit readiness.
Component Suppliers & Firmware Developers
Suppliers of connectivity modules, secure elements, or embedded firmware stacks may face increased demand for auditable security attestations. Their technical specifications—and ability to demonstrate alignment with CPSC’s defined criteria—could become part of procurement evaluation for downstream manufacturers.
Distribution & E-commerce Platforms
U.S.-based distributors and online marketplaces may begin requiring label verification prior to listing or shipment receipt. Non-labeled inventory could be quarantined at fulfillment centers, affecting turnover velocity and channel compliance workflows.
What Relevant Companies or Practitioners Should Focus On Now
Monitor the official CPSC docket and comment deadline
The draft rule remains subject to revision based on stakeholder input. Companies should track Docket No. CPSC-2026-0012 on the CPSC website and note the formal comment period closing date—this is the primary window to influence scope, definitions, or phase-in timing.
Map current product lines against the three required disclosures
Begin internal gap assessment: For each U.S.-bound SKU, verify whether firmware update methods (e.g., OTA vs. manual), documented vulnerability response SLAs (e.g., ≤72-hour acknowledgment), and encryption standards (e.g., TLS 1.2+, AES-256 at rest/in transit) are formally defined, implemented, and testable—not just claimed in marketing materials.
Distinguish between labeling obligation and technical capability
The rule mandates disclosure—not certification or third-party testing—at this stage. A label must reflect actual, operational practices. Companies should avoid conflating voluntary security frameworks (e.g., NIST IR 8259) with the CPSC’s specific, enforceable labeling criteria.
Prepare supply chain communication protocols
Upstream partners—including firmware vendors and chipset suppliers—may need to provide attestation letters or technical summaries to substantiate label claims. Internal SOPs for collecting, archiving, and validating such inputs should be drafted ahead of Q4 2026.
Editorial Perspective / Industry Observation
Observably, this draft rule functions primarily as a regulatory signal—not yet an enforcement mechanism. Its significance lies less in immediate legal force and more in its alignment with broader U.S. federal efforts to treat consumer IoT security as a product safety issue, similar to physical hazard standards. Analysis shows the CPSC is deliberately using labeling as a low-barrier entry point to establish baseline transparency, rather than imposing full lifecycle certification. From an industry perspective, this signals a shift toward traceable, vendor-attested security practices—not theoretical best practices—as a condition of market access.
Current implementation status remains preliminary: no final rule, no approved label format, and no designated verification body. What’s emerging is not a compliance endpoint, but a structured escalation path—starting with disclosure, potentially leading to mandatory updates or breach reporting in future iterations.
Conclusion
This draft rule marks the first formal step by the CPSC to embed verifiable cybersecurity expectations into the U.S. consumer IoT supply chain. It does not introduce new technical standards per se, but instead institutionalizes accountability through mandatory, standardized disclosure. For affected businesses, it is more appropriately understood as an early-stage procedural requirement—one that prioritizes demonstrable process over absolute security perfection. Ongoing attention to the CPSC’s public docket, rather than premature certification spending, represents the most rational near-term posture.

Source Attribution
Main source: U.S. Consumer Product Safety Commission (CPSC), Draft Rule Cybersecurity Labeling Requirements for Internet-Connected Devices, published May 6, 2026. Docket No. CPSC-2026-0012.
Points requiring ongoing observation: Final rule issuance date, approved label format specifications, and any statutory authority expansion beyond CPSC’s current jurisdictional scope.
Get weekly intelligence in your inbox.
No noise. No sponsored content. Pure intelligence.